Violence Prevention Strategies
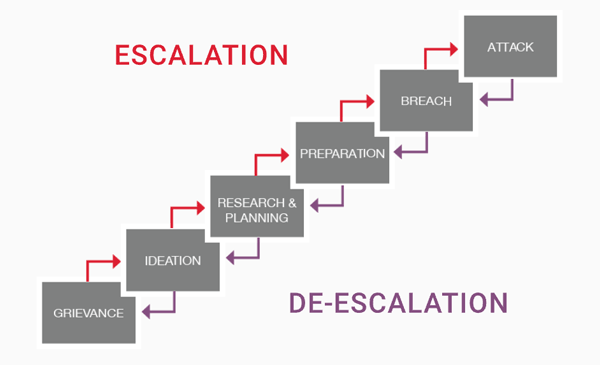
When behaviors of concern have been identified, the appropriate Behavioral Threat Assessment Team may conduct a fact-based behavioral threat assessment and, when necessary, shall alert appropriate university officials, such as the Campus Violence Prevention Committee Based on the assessment, members of the appropriate Behavioral Threat Assessment Team will determine whether they believe a subject (an individual, group, or organization) is on the pathway toward harmful or violent behavior, and the team will determine a level of concern, which guides threat management actions.
Identification Heading link

The identification phase involves the recognition and reporting of behaviors of concern. Anyone may recognize concerning behavior or situations that pose, or have the potential to pose, a threat of violence. When UIC community members or others recognize such behavior/situations, they should immediately report the behavior/situation to the appropriate campus officials (i.e., Behavioral Threat Assessment Teams) using the reporting options described on HERE.
Once the behaviors or situations of concern have been reported to the appropriate Behavioral Threat Assessment Team, the behavior/situation of concern has been “identified.” Additional information on the identification of behaviors of concern is described in the Violence Prevention Plan.
Assessment Heading link

When behaviors of concern have been identified, the appropriate Behavioral Threat Assessment Team may conduct a fact-based behavioral threat assessment and, when necessary, shall alert appropriate university officials, such as the Campus Violence Prevention Committee Based on the assessment, members of the appropriate Behavioral Threat Assessment Team will determine whether they believe a subject (an individual, group, or organization) is on the pathway toward harmful or violent behavior, and the team will determine a level of concern, which guides threat management actions.
Management Heading link

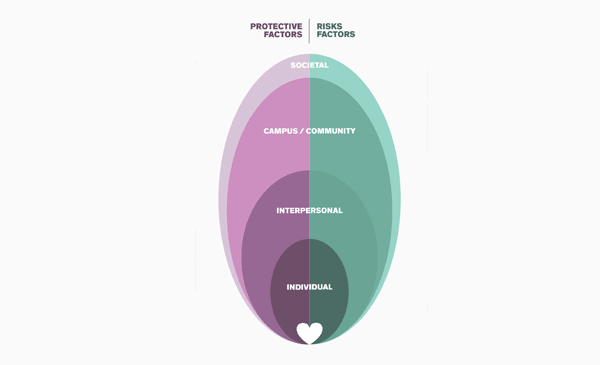
Multiple, concurrent management strategies are almost always appropriate for managing behaviors of concern. Members of Behavioral Threat Assessment Teams identify strategies and resources from the various disciplines represented on the teams, or in the community, to evaluate what can be leveraged toward managing the concerning behavior. There is no “one size fits all” approach to the management of concerning behavior; instead, the team should focus on case-specific, evidence-based solutions predicated upon communication, partnerships, and leveraging of resources.